Introduction
Mitmproxy is a free and open-source interactive SSL-capable proxy that works as man-in-the-middle for HTTP and HTTPS communication. It’s a powerful mitm proxy tool which, according to official documentation, allows you to prettify and decode a variety of message types, intercept specific messages on-the-fly, modify them before they reach their destination, and replay them to a client or server later on.

Mitmproxy can operates in several modes:
- Regular (Default), Transparent, Reverse Proxy, Upstream Proxy, SOCKS Proxy.
mitmproxy: Interactive SSL-capable man-in-the-middle Proxy
It is a swiss-army knife for debugging, testing, privacy measurements and penetration testing, which allows you to intercept, inspect, modify and replay HTTP/1,HTTP/2 traffic, WebSockets and other SSL-protected protocols.
How it works?
Mitmproxy pretends to be the server to the client, and pretend to be the client to the server, while we sit in the middle decoding traffic from both sides.
- The client connects to the proxy and makes a request.
- Mitmproxy connects to the upstream server and simply forwards the request on.
Main mitmproxy features can be used through web-based UI mitmweb, involving interactive examination and modification of HTTP traffic. In addition, there is a Python API, which makes mitmproxy highly configurable. It offers full control and makes it possible to automatically modify messages, redirect traffic, visualize messages, or implement custom commands.
Features:
- Intercept HTTP & HTTPS requests and responses and modify them on the fly
- Save complete HTTP conversations for later replay and analysis
- Replay the client-side of an HTTP conversations
- Replay HTTP responses of a previously recorded server
- Reverse proxy mode to forward traffic to a specified server
- Transparent proxy mode on OSX and Linux
- Make scripted changes to HTTP traffic using Python
- SSL/TLS certificates for interception are generated on the fly
- etc.
Tools:
mitmproxy
Interactive MiTM proxy for HTTP/HTTPS with a console interface.mitmdump
Command-line version of mitmproxy. Think tcpdump for HTTP.mitmweb
Web-based interface for mitmproxy. (currently in beta)Requirements:
Python 3.6+(in order to run the latest version)requirements.txt
Install
Linux:
First of all, you need to make sure that you’ve installed the latest Python version. Then clone mirmproxy from the GitHub repo:
$ git clone https://github.com/mitmproxy/mitmproxy.git
Navigate to the working directory, and run ./dev.sh script:
$ cd mitmproxy
$ ./dev.sh
dev script will create a virtualenv environment in a directory called venv and install all mandatory and optional dependencies into it.Now you can install it via pip3:
$ pip3 install mitmproxy
OS X:
Use Homebrew to install mitmproxy (recommended):
$ brew install mitmproxy
If you don’t have Homebrew installed, you can do it by running the following command:
$ /usr/bin/ruby -e "$(curl -fsSL https://raw.githubusercontent.com/Homebrew/install/master/install)"
Docker:
You can use the official mitmproxy images from DockerHub.
Usage
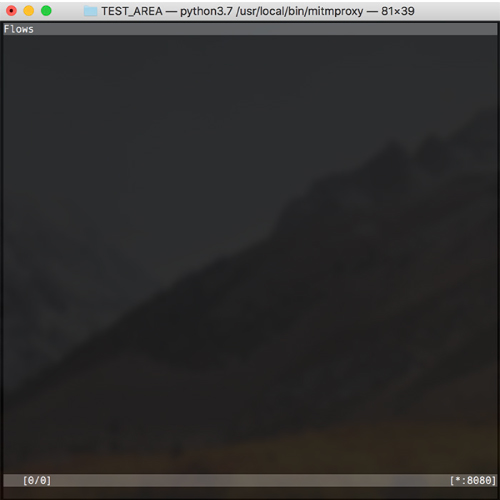
To start using it, just runmitmproxy, and you should see a welcome screen:
To list all available options, use --help:

Given that these are just some basic information about the mitmproxy, we’ll make sure to write about practical usage in some of the future posts. For detailed explanation and installation examples, click the “documentation” button below.



![Modlishka: Powerful Reverse Proxy [Phishing NG, Bypassing 2FA] Modlishka: Powerful Reverse Proxy [Phishing NG, Bypassing 2FA]](https://cdn.cyberpunk.rs/wp-content/uploads/2019/01/modlishka_phishing_bg-500x275.jpg)

